Security teams rarely struggle with visibility alone. They struggle with time, context, and confidence. Alerts arrive in volume. Tools generate data. Analysts make judgement calls under pressure. What tends to break down is not technology, but coordination and speed.
Understanding how CrowdStrike MDR handles incident detection and response requires looking beyond feature lists. It is less about dashboards and more about how decisions are made when something suspicious surfaces randomly.
CrowdStrike built its managed detection and response capability around a simple reality. Most organisations cannot maintain 24-hour detection engineering, threat intelligence correlation and rapid containment internally without burning out their teams. MDR, when done properly, becomes an extension of operational security rather than an outsourced alert desk.
The mechanics matter. But so does the human layer wrapped around them.
The Foundation: Telemetry Without Noise
Endpoint detection tools have matured. Raw data is not the problem anymore. The difficulty lies in turning millions of signals into meaningful detection without overwhelming analysts.
CrowdStrike MDR operates on top of its Falcon platform. That platform already captures process activity, network connections, identity behaviour, and lateral movement indicators at scale. The MDR layer sits over this and introduces continuous analyst review combined with curated detection logic.
What stands out is the filtering discipline.
Rather than forwarding every suspicious behaviour to a customer SOC, the MDR team applies layered triage. Automated logic removes obvious false positives. Human analysts then assess what remains. This is not glamorous work. It is slow, pattern-based, and often repetitive. Yet it is where fatigue normally creeps in for internal teams.
By centralising that burden, the service reduces the volume that customers need to investigate themselves. The aim is not to eliminate alerts. It is to reduce ambiguity.
In practice, this means incidents reaching the client already carry context. Process trees are reconstructed. Command lines are examined. External intelligence is correlated quietly in the background.
There is less guesswork left for the organisation consuming the alert.
Detection is Not a Single Moment
Many discussions around incident response focus on the “point of detection” as though compromise is a switch being flipped. Reality doesn’t behave so neatly.
Detection often unfolds in stages. An anomalous PowerShell execution might look harmless in isolation. Add credential dumping activity thirty minutes later, and the pattern sharpens.
CrowdStrike MDR handles detection as an evolving narrative instead of a single trigger. Analysts review behavioural chains over time. Telemetry from endpoints, identity logs and cloud workloads is correlated continuously. Suspicion strengthens or weakens as more data arrives.
This layered view helps avoid both panic and complacency. It also reduces the risk of reacting aggressively to benign administrative activity.
In environments with heavy automation and DevOps pipelines, that distinction matters. Overreaction can disrupt production faster than the attacker ever would.
The Human Decision Point
Automation accelerates analysis. It does not replace judgement.
One of the consistent weaknesses in internal SOCs is escalation paralysis. Analysts see something odd but hesitate. Is this malicious? Is it worth waking someone up? Should containment begin immediately?
CrowdStrike MDR operates with predefined containment authority agreed in advance with the client. That clarity removes hesitation. When malicious activity crosses agreed thresholds, containment actions such as host isolation can be triggered rapidly.
There is something important here. Speed without coordination causes friction. Coordination without speed invites damage.
The service attempts to balance both by defining response playbooks upfront. These are not rigid scripts. They are boundaries within which analysts operate confidently.
The difference becomes obvious during active ransomware activity. Lateral movement spreads quickly. Waiting for multi-layer approval chains can cost hours. MDR analysts can isolate hosts, kill processes and prevent further encryption while communication continues with the client.
This does not eliminate business impact. It narrows the blast radius.
How Incident Response Unfolds in Practice
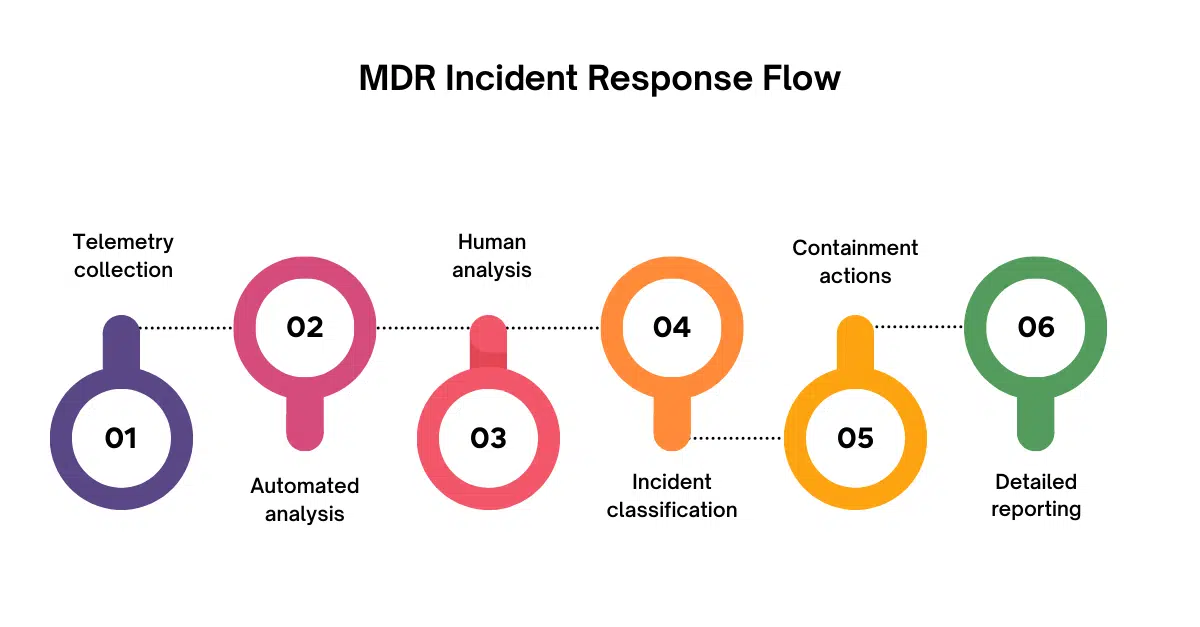
Below is a simplified representation of how incident detection and response typically progresses within the MDR framework:
- Telemetry collection across endpoints, identities, and cloud assets
- Automated behavioural analysis and threat intelligence correlation
- Human analyst triage to validate suspicious activity
- Incident classification with severity and impact assessment
- Containment actions such as host isolation or credential revocation
- Detailed reporting with forensic context and remediation guidance
This is not a linear path. Analysts move back and forth between steps as evidence develops. Sometimes a suspected intrusion collapses into a benign administrative action. Other times an initially low severity alert escalates quickly after additional artefacts surface.
The key is continuity. The same team follows the incident through rather than handing it between disconnected functions.
Threat Intelligence Woven into Detection
Threat intelligence only becomes useful when it alters decision-making.
CrowdStrike’s MDR service integrates global threat research into detection logic. Indicators linked to active campaigns are fed into behavioural analytics. This does not mean relying solely on known hashes or IP addresses. Most serious attackers rotate infrastructure quickly.
Instead, intelligence informs patterns. Techniques observed in recent intrusions influence how telemetry is interpreted. A sequence of commands that might otherwise look generic can gain weight when aligned with current adversary tradecraft.
This is subtle work. It does not show up as a dramatic banner on a console. Yet it strengthens early detection, especially in targeted attacks where traditional signature matching fails.
For organisations without dedicated threat intelligence teams, this external perspective closes a blind spot.
Transparency During Containment
Incident response frequently breaks down during communication. Technical teams focus on stopping the threat. Leadership demands clarity. Legal teams want to understand exposure. Mismatched language creates friction.
MDR engagements typically provide structured incident reporting alongside real time updates. Containment steps are documented clearly. Evidence supporting decisions is summarised in practical terms.
What matters here is traceability. Clients can see why a host was isolated, which artefacts triggered escalation, and what remediation steps are required. This transparency builds trust. Without it, outsourced response feels opaque.
In longer investigations, such as data exfiltration cases, MDR analysts often support deeper forensic analysis. The platform’s telemetry retention assists reconstruction. Timeline clarity becomes crucial if regulatory notification is required.
Again, the strength lies less in tooling and more in disciplined analysis.
Limitations and Realistic Expectations
It would be unrealistic to assume any MDR service prevents every breach. Attackers adapt. Business environments evolve. Misconfigurations introduce new attack paths.
MDR improves detection and response maturity. It does not replace internal security ownership. Organisations still need asset visibility, clear escalation paths and executive support during incidents.
There are also cultural considerations. Some security leaders initially resist granting containment authority to an external team. That hesitation is understandable. Handing over the ability to isolate production systems requires trust and clear scoping.
When implemented thoughtfully, with defined boundaries and periodic review, the model tends to settle into a steady rhythm. Internal teams focus more on strategic risk reduction. MDR absorbs the constant alert pressure.
The balance will vary by organisation size and risk appetite.
Operational Maturity Over Tool Dependency
The conversation around how CrowdStrike MDR handles incident detection and response often drifts towards platform capability. In practice, operational maturity shapes outcomes more than feature depth.
Clear runbooks. Pre-agreed authority. Consistent communication. Realistic service level expectations.
Without these, even advanced tooling produces friction.
When these elements align, detection becomes sharper and response becomes faster without descending into chaos.
It is worth pausing here. Technology enables response. Process and people determine whether it works under stress.
Conclusion
Understanding how CrowdStrike MDR handles incident detection and response requires looking beyond marketing descriptions. The strength lies in disciplined triage, contextual analysis and predefined containment authority. Detection is treated as a narrative that develops over time, not a single flashing alert. Response focuses on speed without sacrificing traceability.
For organisations weighing whether MDR fits their operating model, the decision is rarely about capability alone. It is about trust, control, and how much internal resource can realistically be sustained.
CyberNX can help you with CrowdStrike consulting effectively and help you get full value from Falcon platform. They design and manage Falcon in your environment – with 24×7 support and MDR to respond to threats anytime.
Handled properly, MDR becomes less about outsourcing security and more about reinforcing it with steady, experienced hands.